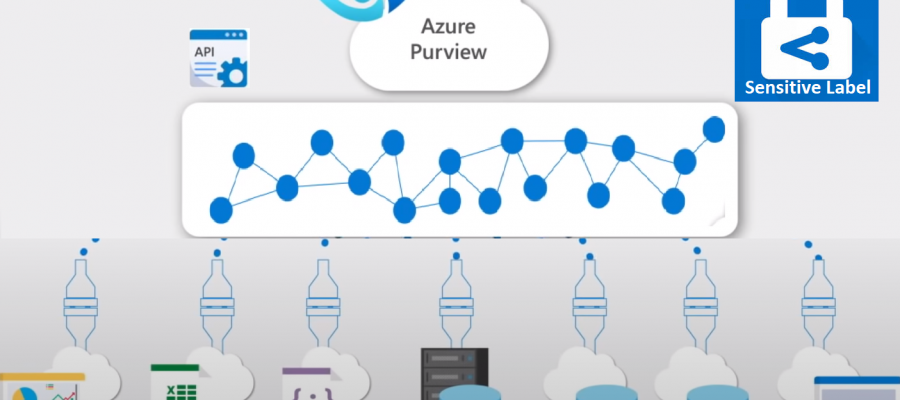
Azure Purview enables you to map, catalogue, understand, classify, and manage your operational and analytical data—whether on-premises, across your multi-cloud environment or within SaaS applications. With Purview Data Catalog, you can now search, understand the underlying sensitivity, and view how data is being used across the organization with data lineage.
Microsoft Information Protection, a built-in, intelligent, unified, and extensible solution that understands and classifies your data, keeps it protected, and prevents data loss across Microsoft 365 Apps (including Word, PowerPoint, Excel, Outlook), services (such as Microsoft Teams, SharePoint, Exchange, Power BI), third-party SaaS applications, and more—on-premises or in the cloud.
Sensitivity Labels enables you to state how sensitive certain data is in your organization. W~hen your data roam, inside or outside the organisation; you want it to do so in a secure, protected way that meets your organization’s business and compliance policies. For example, a specific project name might be highly confidential within your organization, while that same term is not confidential to other organizations.
MIP sensitivity labels are created in the Microsoft 365 Security and Compliance Center (SCC). Purview uses the same classifications, also known as sensitive information types, like Microsoft 365. This enables you to extend your existing sensitivity labels across your Azure Purview assets. Microsoft Information Protection’s sensitivity labels with Azure Purview, organizations can now automatically discover, classify, and get insight into sensitivity across a broader range of data sources such as SQL Server, SAP, Teradata, Azure Data Services, and Amazon AWS S3, helping to minimize compliance risk.
Auto labelling rules are conditions that you specify, stating when a particular label should be applied. When these conditions are met, the label is automatically assigned to the data, retaining consistent sensitivity labels on your data, at scale.
Create and Deploy Auto Labelling
MIP sensitivity labels are only available for assets in Microsoft 365, where you can apply them to files and emails. To apply MIP sensitivity labels to Azure assets in Azure Purview, you must explicitly consent to extending the labels, and select the specific labels that you want to be available in Purview. Consenting in Microsoft 365 compliance center applies to sharing this data with both services.
- Make sure to create or modify existing sensitive labels.
- Make them available for Azure Purview
- Define auto labelling rules for both files and database columns to apply your labels automatically with each data scan.
- After scanning your data in Purview, you can view the labels automatically applied in the Purview Catalog and Insight reports.
Sensitivity labels are supported in Azure Purview for the following data types:
| Data type | Sources |
|---|---|
| Automatic labeling for files | – Azure Blob Storage – Azure Data Lake Storage Gen 1 and Gen 2 |
| Automatic labeling for database columns | – SQL server – Azure SQL database – Azure SQL Database Managed Instance – Azure Synapse – Azure Cosmos DB |
To extend sensitivity labels to Purview:
In Microsoft 365, navigate to the Information Protection page. In the Extend labeling to assets in Azure Purview, select the Turn on button, and then select Yes in the confirmation dialog that appears.
Licensing requirements:
MIP sensitivity labels are created and managed in the Microsoft 365 Security and Compliance Center. To create sensitivity labels for use in Azure Purview, you must have an active Microsoft 365 E5 license.